Think of SPECTER as a private mailbox system. You put up a public sign that says “send mail here,” but every letter gets routed to a different, secret mailbox that only you can open.
SPECTER is not a chain, a token, or a new wallet
It’s a private receiving layer. You publish one public profile, and each sender turns it into a different one-time address. To everyone else, the payment lands at an address that looks unrelated to you.Three concepts, that’s it
1. Meta-address (your public profile)
Your meta-address is what you share with the world. It contains two public keys:- Spending public key - used to derive where the money goes
- Viewing public key - used to create a shared secret with the sender
alice.eth) or SuiNS name (alice.sui) so senders just need to know your name.
2. Stealth address (the one-time destination)
When someone wants to pay you, they take your meta-address and mathematically derive a brand-new address. This address has never appeared on-chain before and can’t be linked back to your meta-address without your private keys. The sender sends ETH or tokens to this address. Done.3. Announcement (the coded breadcrumb)
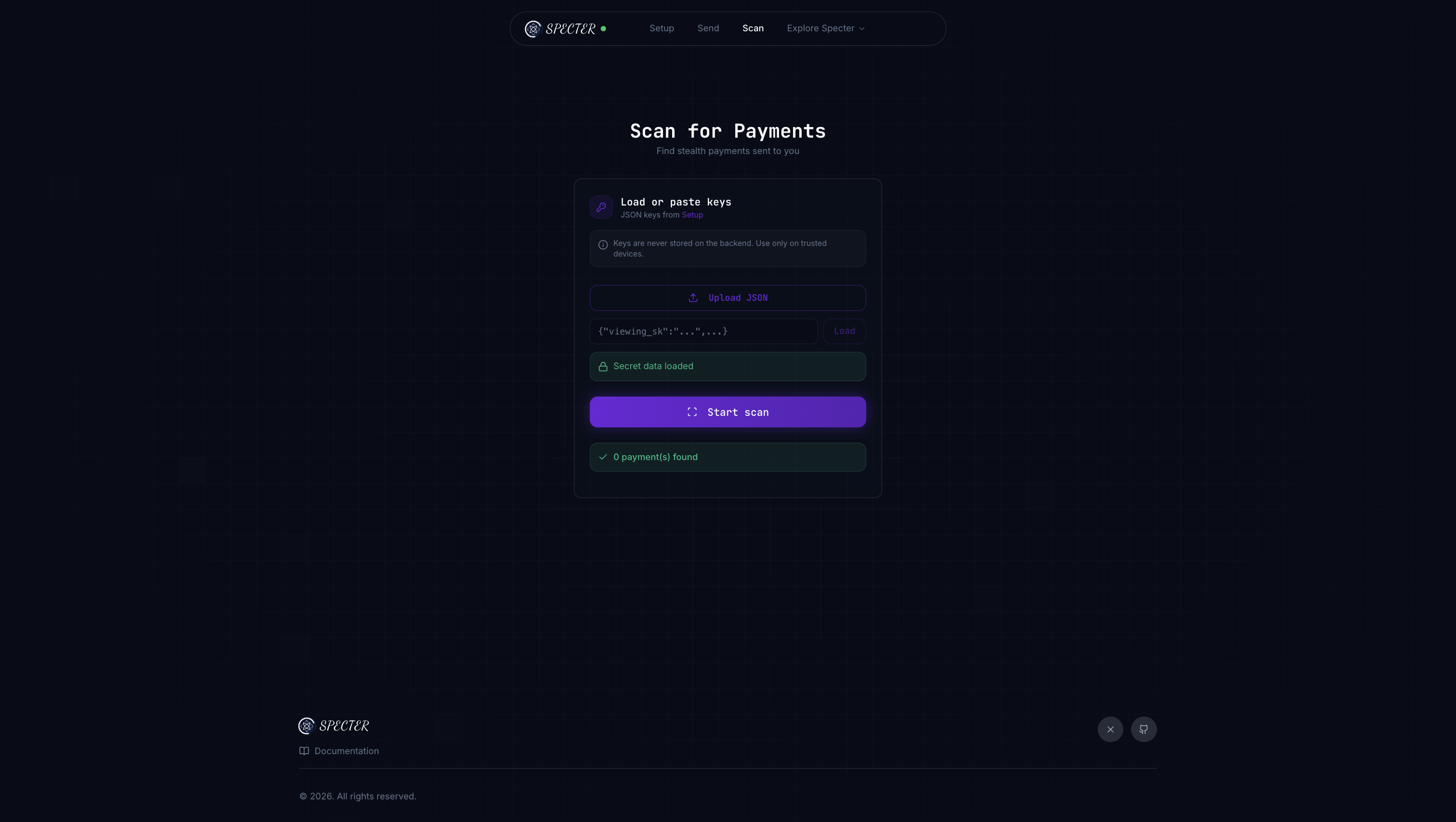
After sending, the sender posts a small piece of data (an announcement) that contains an encrypted hint. You can scan all announcements using your private viewing key, quickly filter out the ones that aren’t for you, and find your payments.The full flow in one picture

Step by step
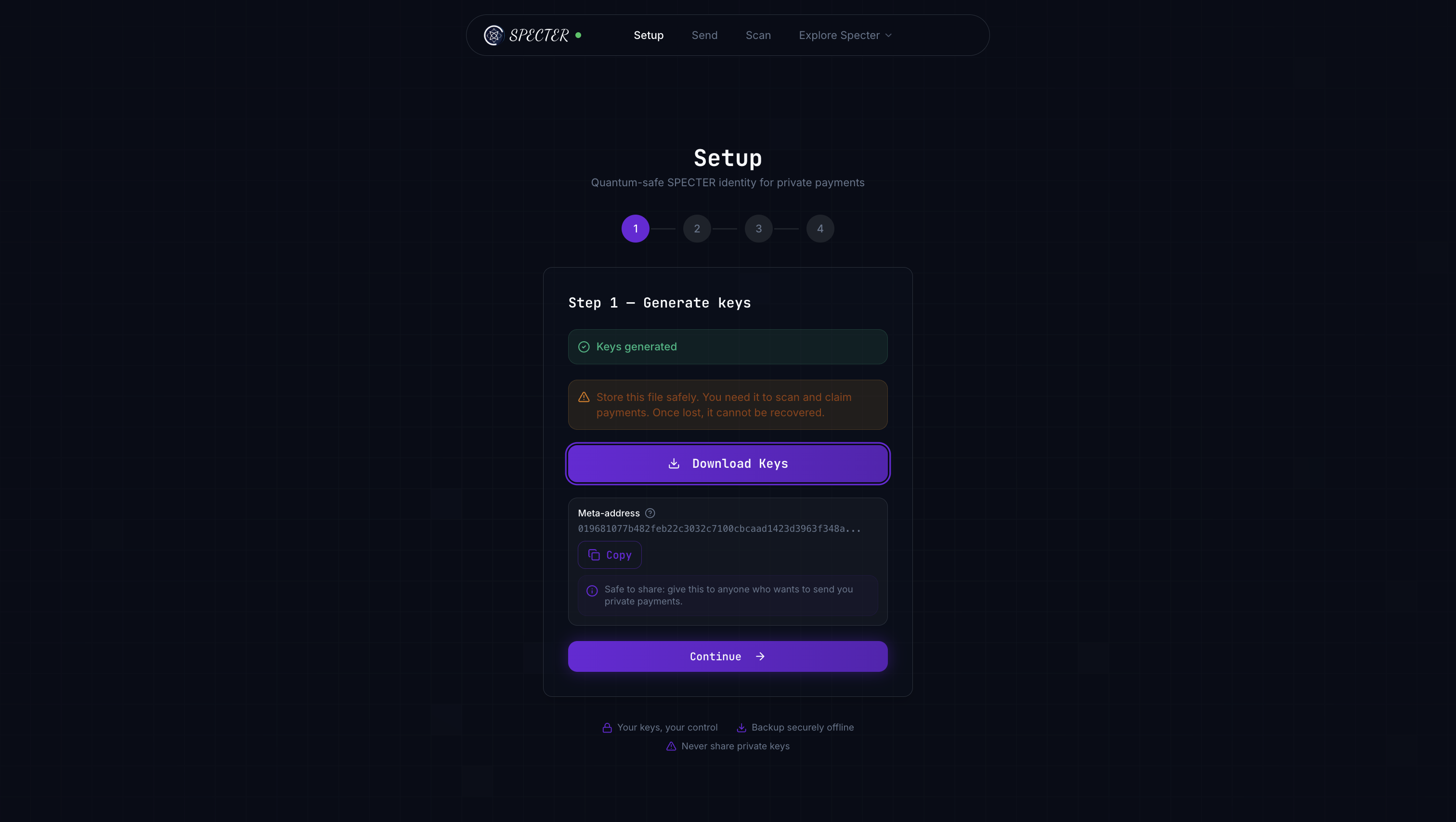
Set up your profile
Generate your ML-KEM key pairs (spending + viewing). Bundle the public keys into a meta-address. Optionally link it to your ENS or SuiNS name.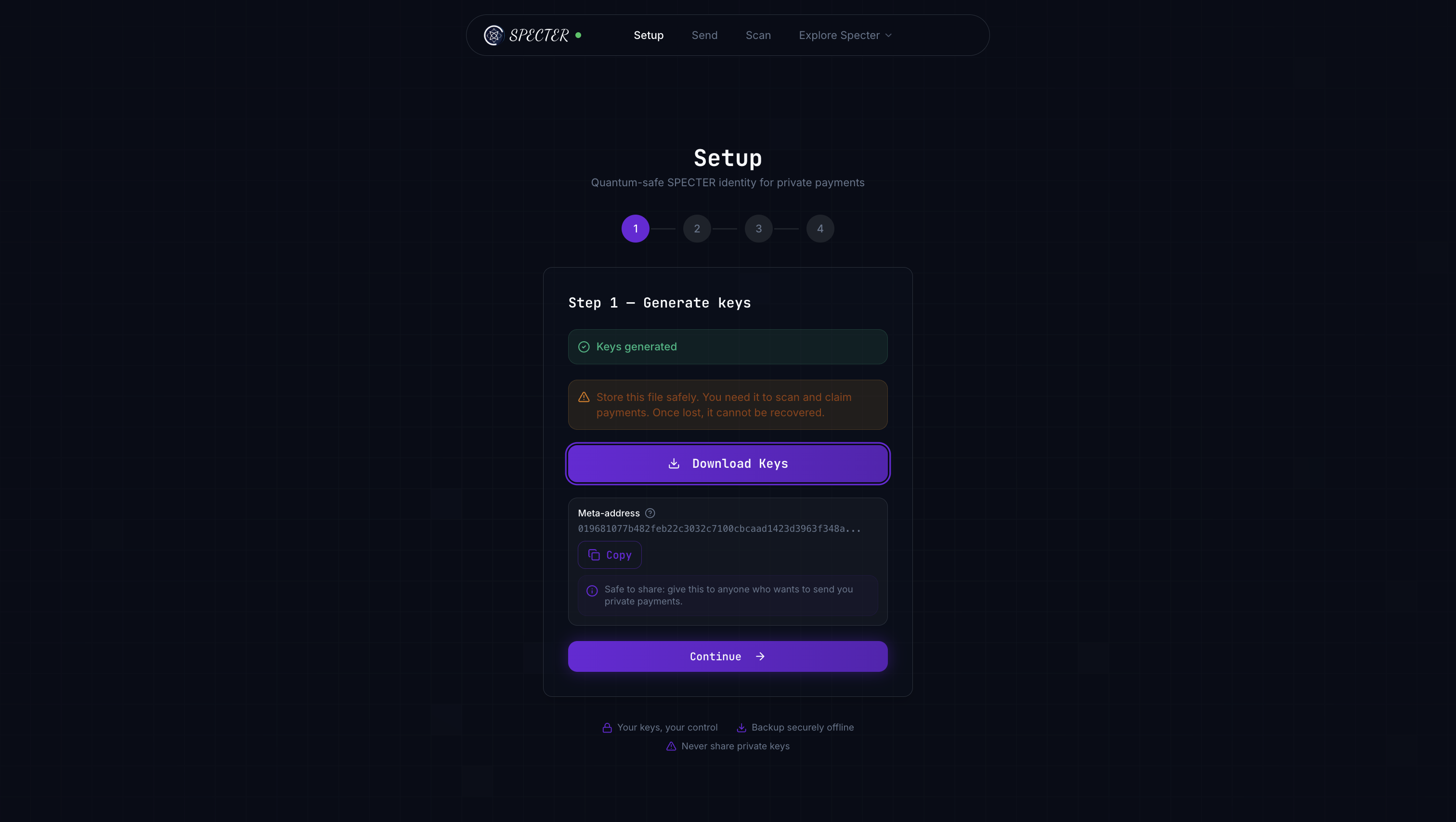
Sender creates a payment
The sender fetches your meta-address, runs ML-KEM encapsulation to create a shared secret, and derives a fresh stealth address from it. They also compute a 1-byte view tag for fast filtering.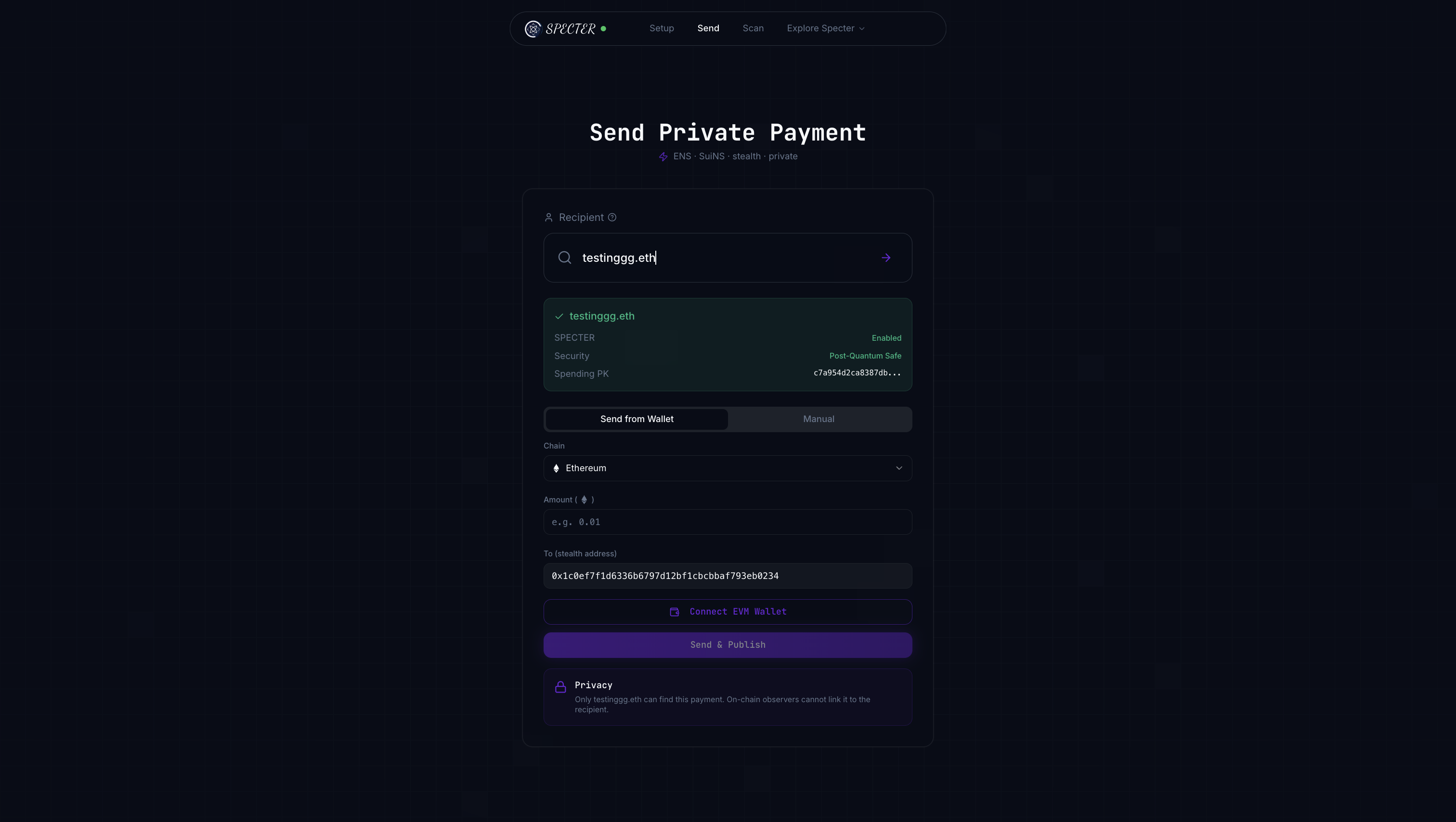
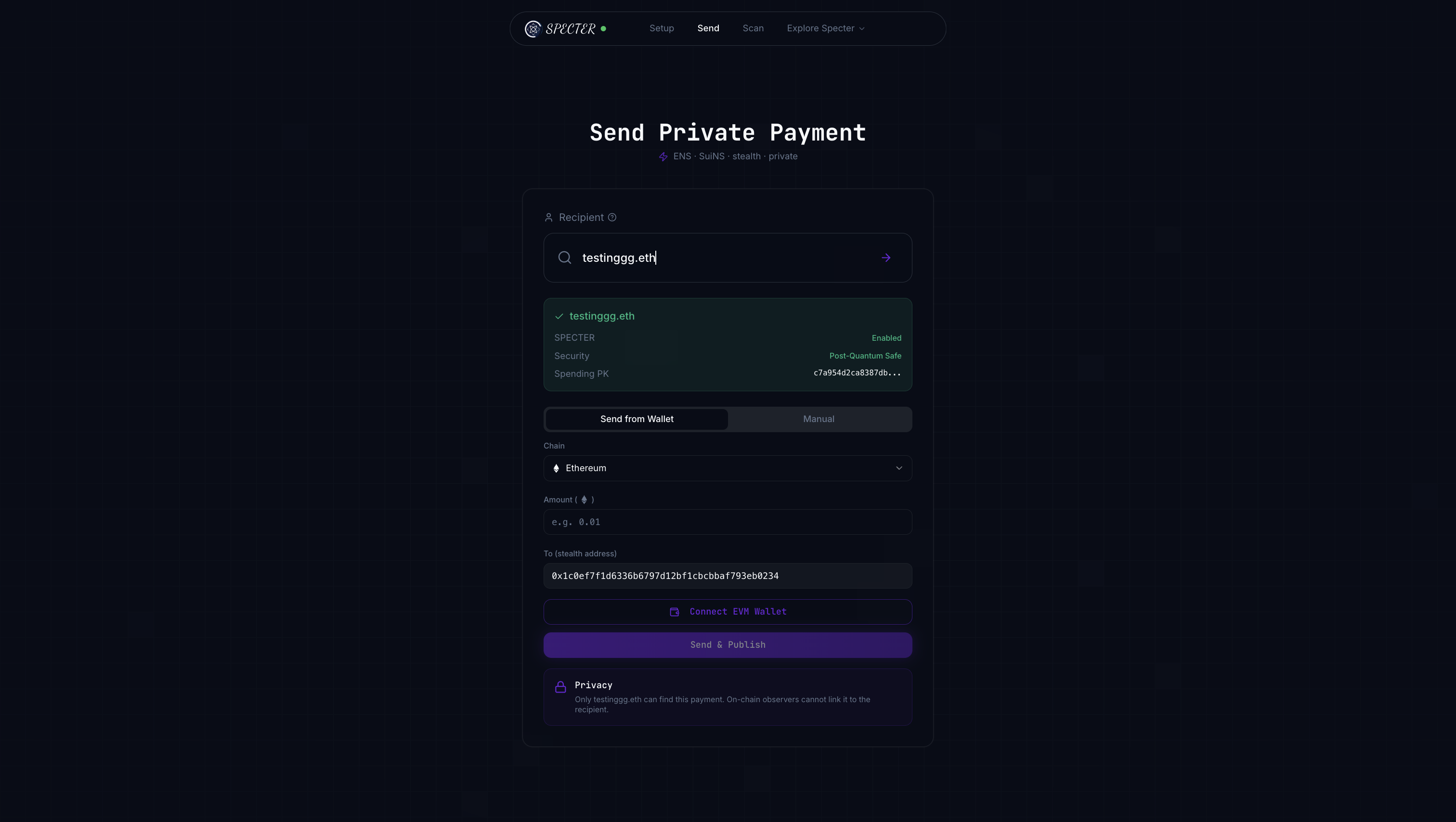
Sender posts an announcement
The sender publishes the encrypted ciphertext and view tag to the announcement registry. This is the breadcrumb you’ll use to find the payment.
What makes this post-quantum?
The shared secret between sender and recipient is created using ML-KEM-768, not classical ECDH. ML-KEM is based on lattice math that quantum computers can’t efficiently crack (no known algorithm exists). The ciphertext sitting on-chain is safe even against future quantum attackers.
The honest picture
What you should read next
Full protocol flow
Every step with code references and diagrams.
Try it yourself
Hit the live API and see it work.
SPECTER vs others
How we compare to Umbra and Fluidkey.